Table of Contents
Get effective instructions on removing the Virus Alert from Apple scam and learn what risks the related malware poses to Mac users.
What is the Virus Alert from Apple scam?
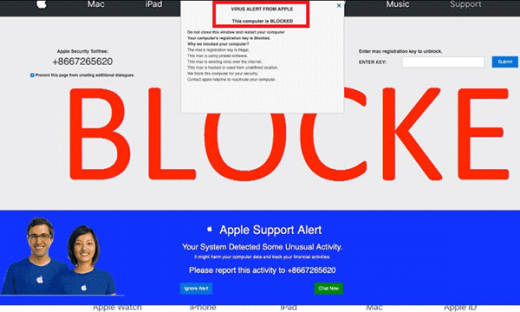
The Virus Alert from Apple popup notification is the pivot of an ongoing hoax that targets Mac users. Its goal is to scare the victim into thinking their computer is severely damaged and sticking with a “This Mac computer is blocked” warning message and recommendation to contact “tech personnel” who are fraudsters in disguise. The misleading alert pops up on a malicious website camouflaged as an Apple support related resource. The page mimics the company logo, and some design elements are reminiscent of the genuine style everyone is familiar with. However, the first big giveaway is the URL that has nothing to do with Apple. Secondly, the actual provider will never engage in warning practices as abominable and obtrusive as this. Ultimately, the objective of this ruse is to persuade the user to give the wrong people a phone call.
Let’s now have a look at how exactly this scheme works. It usually starts with a questionably reasonable app installation the would-be victim performs. This routine involves a software bundle that drags several programs into the Mac rather than just one clearly mentioned on the setup client’s screen. While there is nothing illegal about such a package-based promotion, cybercriminals often weaponize it by adding harmful apps to the combo. In the scenario under scrutiny, the user unknowingly allows a piece of malware to infiltrate their Mac while being confident that the only item being installed is some freeware with a couple of nifty features on board. Therefore, it always makes sense to treat bundles with caution and at least opt out of the default install mode so that the possible extras are disclosed and can be deselected. Getting back to the point, the furtively downloaded infection instantly determines which web browser is the victim’s preferred one and unleashes its predefined disruptive power. In particular, it embeds a new plugin that turns the custom web surfing settings upside down.
Having adjusted the browser’s activity to its mission, the predatory code starts forwarding the hijacked traffic to a rogue site hosting the Virus Alert from Apple popups. These domains get blacklisted once in a while, so the URLs will vary. But, as mentioned above, the address is in no way affiliated with Apple, and fortunately, it doesn’t take a scientist to identify this major clue suggesting that it’s a scam. The fake alert on the page says the Mac has been blocked because of a virus that the user caught when visiting a porn site. It goes on to stress that Apple has locked down the computer to prevent the infection from spreading further and thwart detrimental consequences for the user.
The main tip on the phony site regarding the fix is to call the pseudo tech support or start a conversation with them via the built-in chat widget. However, if the swindlers are contacted they will most likely instruct the victim to give them remote access to the system so that they can supposedly repair it and eliminate the “virus”. In actuality, by gaining a foothold on the Mac this way, the crooks will install more malware and demand a fee for the troubleshooting. Therefore, in case you are still curious whether it’s a good idea to reach out to the operators of the Pornographic Virus Alert from Apple popup scam, the answer is a big “No”. Instead, get rid of the misbehaving entity that causes the browser redirects in the first place.
Automatic removal of the Virus Alert from Apple scam
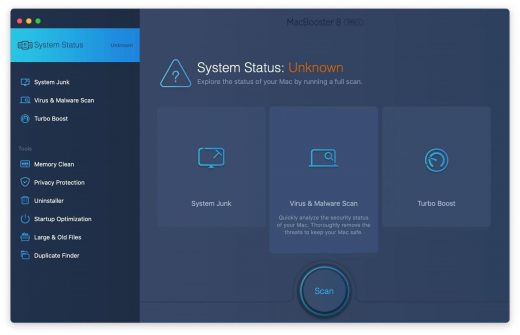
If this threat has infected your Mac, the most effective way to get rid of it is to use an automatic cleaning tool. The main benefit of taking this route is that the security application will accurately pinpoint and remove all the malicious files, including hidden components that could be difficult to find and erase manually. MacBooster is an award-winning solution that makes this process easy and fast. Follow the steps below to make the most of its malware removal and optimization power:
1. Download and install MacBooster onto your Mac.Download Virus Alert virus removal tool
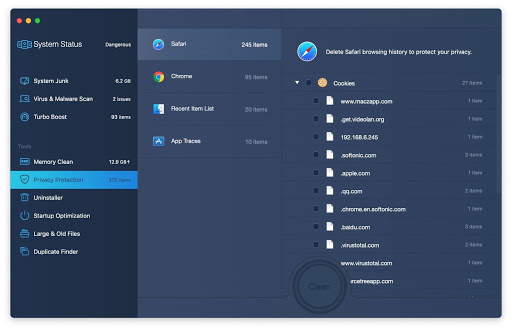
2. Open the tool and click on the Scan button on its home screen called System Status. The application will check your Mac for viruses and malware, memory issues, and junk files. 3. Once the scan is completed, MacBooster will display a report listing all the security and performance problems detected on your computer. Click on the Fix button to remove the malicious items and fine-tune your Mac’s performance.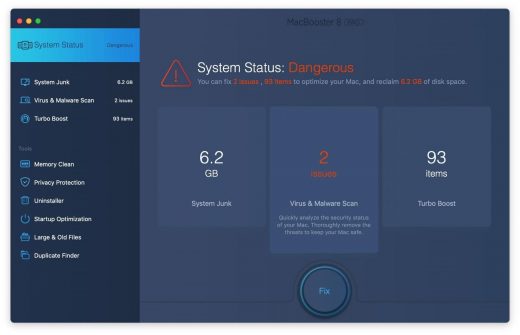 4. To address the after-effects of Virus Alert virus activity in the web browser, select the Privacy Protection feature in MacBooster sidebar, choose your default browser, and click on the
Clean button at the bottom. This will delete unwanted cookies and other items affecting the browser behavior.
4. To address the after-effects of Virus Alert virus activity in the web browser, select the Privacy Protection feature in MacBooster sidebar, choose your default browser, and click on the
Clean button at the bottom. This will delete unwanted cookies and other items affecting the browser behavior.
The Virus Alert virus shouldn’t be messing around with your Mac any longer. Be advised, though, that your default browser may still be redirected to dubious pages until you rectify its settings (the reset procedure will be described further down).
Virus Alert from Apple hoax manual removal
The gist of this section is to walk you through the process of deleting all non-obfuscated files related to the Virus Alert virus Mac. It’s best to perform the cleanup in the order specified below.
-
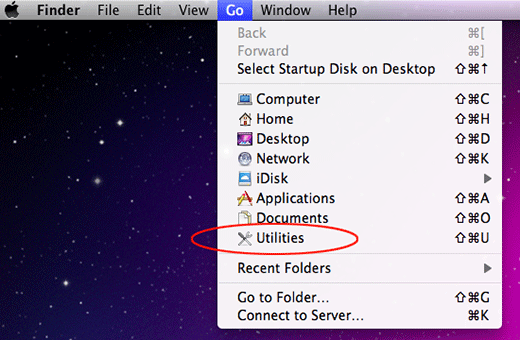
Click the Go icon in Finder and select Utilities on the list

-
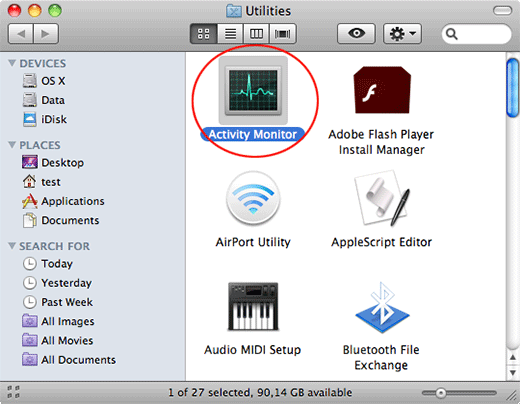
Find and select the Activity Monitor under Utilities

-
In the Activity Monitor, scrutinize the running processes for one that consumes lots of CPU and looks suspicious. Once the likely baddie is found, select it and click the Quit Process icon. An additional
confirmation dialog will pop up – click Force Quit on it

-
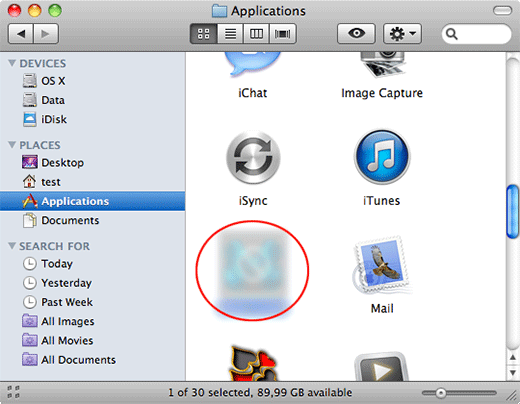
Now, go to Applications under the Go menu

-
What you need to do is scroll down the list of installed apps in search of the malicious item. It could be a program with a gibberish name or one that ended up on your Mac beyond your awareness

-
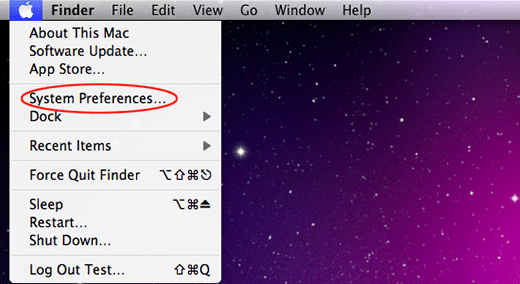
Go to System Preferences as shown below

-
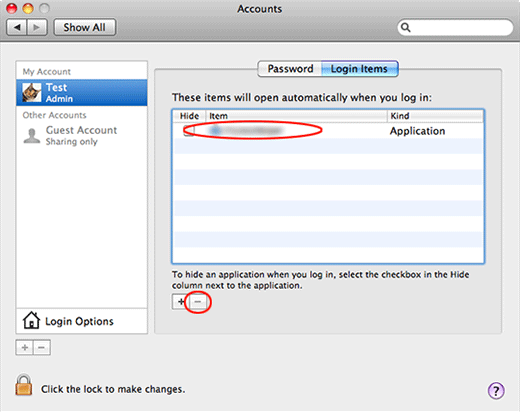
Select Accounts, then Login Items. You will see all the apps that run as part of the Mac startup process. Find the infection and remove it from the list by means of the “minus” icon

Now that you have suppressed the virus proper, you need to fix the problem in Safari. The browser defaults continue to be set to Virus Alert, therefore the repair requires some manual configuration tweaking.
Remove Virus Alert from Apple scam in web browser
The optimal troubleshooting method boils down to resetting the browser, which will undo all changes made by the infection or any third-party plugin without your permission. Here’s how to do it:
Reset Safari to its defaults
-
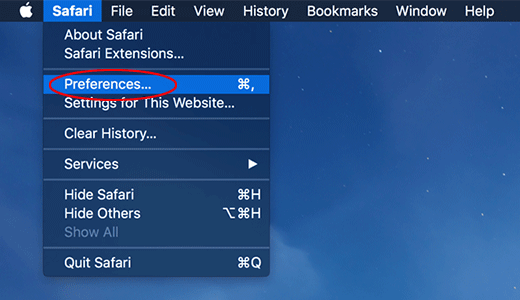
Go to Safari menu bar and select Preferences again on the drop-down list

-
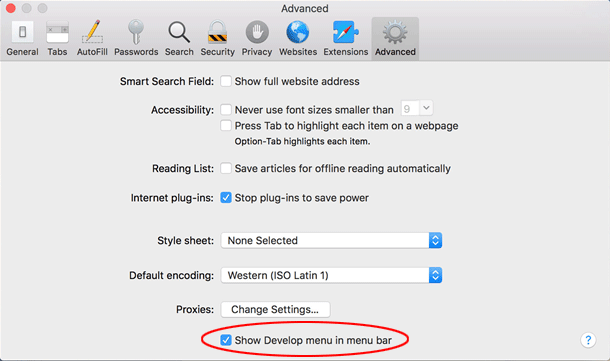
Go to Advanced tab and enable the option that says Show Develop menu in menu bar

-
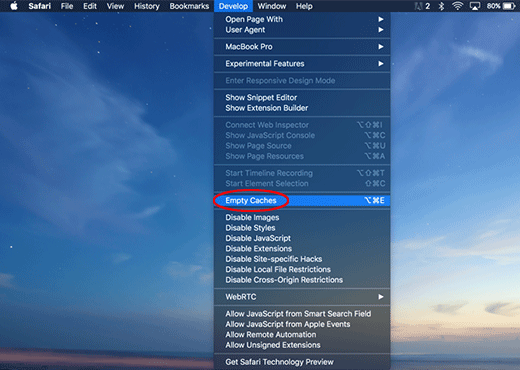
Now you will see the extra Develop menu in your Safari menu bar. Click it and select Empty Caches as shown below

-
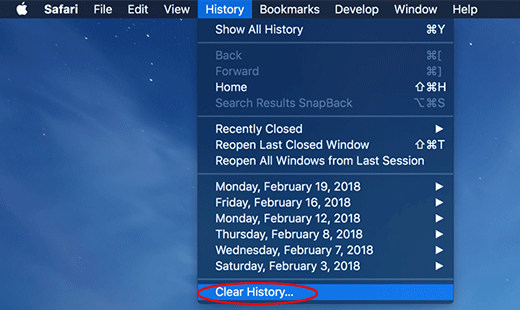
Do some test browsing to see if things are okay now and whether the malware is gone. If the issue is still there, you may need to additionally clear your browsing history in Safari. In Safari menu bar, select
History and click Clear History

-
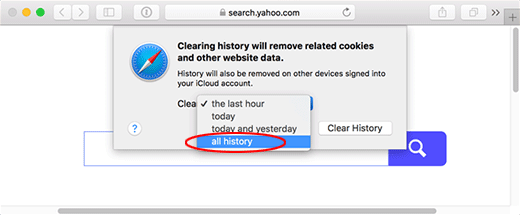
The browser will display a dialog so that you can select the required period you would like to clear history for. Select all history on the list and click the Clear History button

-
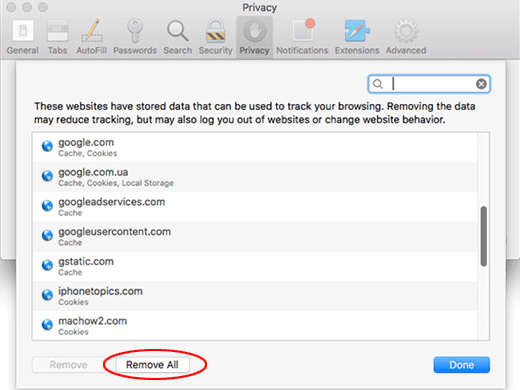
In case Safari is still acting up due to malware interference, there is one more thing you can try. Once again, go to Preferences from the Safari menu bar and select the Privacy tab
this time. Click Manage Website Data

-
When Safari generates a full list of sites that have stored your browsing data, go ahead and click Remove All

- Confirm by hitting the Done button.
Reset Google Chrome
- Click More (⁝ icon) at the top right part of the Chrome window and select Settings
- Find the Advanced section on the Settings screen and expand it
-
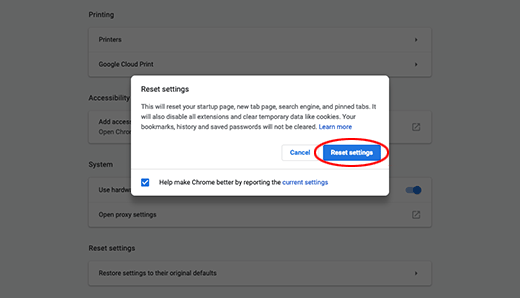
Locate the Reset settings subsection and click Restore settings to their original defaults

- Google Chrome will display a popup dialog asking you to confirm the reset. Click the Reset settings button on it. Now, restart the browser and ascertain that the problem has been fixed.
Refresh Mozilla Firefox
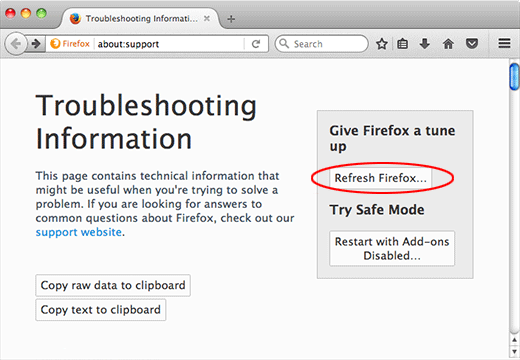
- Go to Help -> Troubleshooting Information, or type about:support in the Firefox URL bar
-
Once the Troubleshooting Information screen appears, find and click the Refresh Firefox button as shown

- Confirm the browser refresh on a dialog that will appear. Restart Firefox and check it for signs of malware tampering.