Table of Contents
This write-up provides an extensive analysis of the Odin ransomware, including details about its encryption routine and ways to restore .odin files.
Imagine a mishap where some unknown entity denies access to all valuable files on one’s Windows computer all of a sudden. Looking into the issue for a minute or two reveals that the impact is selective as it only applies to personal data and keeps system executables intact. Furthermore, no hardware failure is in place. The only thing that causes this sort of damage is crypto ransomware such as Locky that is now changing the file extensions to .odin.
This sample attacks a PC over a spam email attachment, finds the victim’s sensitive files, encrypts them with RSA and AES algorithms, and then demands about 300 USD (may vary) paid in Bitcoins for the unencrypt job. The byproduct of this process is the concatenation of the .odin string at the end of the filenames. This infection targets about a hundred different file types, which it locates inside a contaminated computer based on their extensions. As a result, most of the important data ends up completely scrambled.
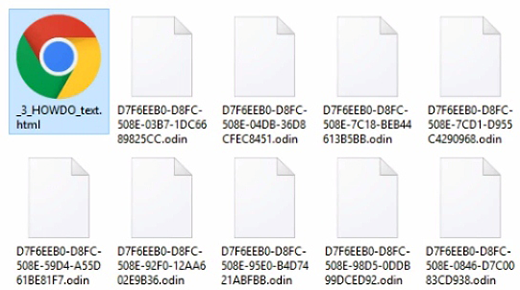
The .odin file virus has a far-reaching adverse effect in terms of the attack surface. Not only does it affect data stored on the local hard drive, but it also looks for proprietary information on mapped network shares, cloud drives and removable media. The cryptosystem it uses is an asymmetric cipher with a public-private key pair being generated for every victim. Recovery is, therefore, a function of the availability of the private decryption key. The hurdle here is that this chunk of data resides outside of the plagued PC, so retrieving it is only doable via interacting with the extortionists who run the secret server with the database of keys. This ‘victim – attacker’ communication is indirect, where the user gets decryption instructions in documents named _HOWDO_text.html and _HOWDO_text.bmp.
Inside the Locky ransom messages are weblinks to a site called the Locky Decryptor Page. This page includes details on the quantity of Bitcoins to submit as a ransom, tips on how to buy the Bitcoins, and the Bitcoin address you must forward the payment to. As soon as a target transmits the payment to the designated Bitcoin address, this website will provide an automatic decrypter which can supposedly be leveraged to decrypt the locked files.
However, this is playing with fire, so it’s recommended to get busy trying alternative recovery measures once the breach takes place. The best-case recovery scenario is to have an offsite backup from which the unmodified data can be safely downloaded. If it’s available, make sure the ransomware code proper is completely wiped off the hard drive. Otherwise, the use of Shadow Copies and special recovery tools is worthwhile.
Automatic removal of .odin file virus
When it comes to handling infections like this one, using a reputable cleaning tool is the place to start. Sticking to this workflow ensures that every component of the adware gets found and eradicated from the affected computer.
1. Download and install the cleaning tool and click the Start Computer Scan button Download ODIN removal tool
2. The wait is worth it. Once the scan completes, you will see a report listing all malicious or potentially unwanted objects detected on your PC. Go ahead and click the Fix Threats option in order to get ODIN automatically uninstalled from your machine. The following steps are intended to restore the encrypted files.
Recover .odin files ciphered by Locky ransomware
Removing the infection proper is only a part of the fix, because the seized personal information will stay encrypted regardless. Review and try the methods below to get a chance of restoring the files.
Option 1: BackupsThe cloud works wonders when it comes to troubleshooting in the framework of ransomware assault. If you have been keeping data backups in a remote place, just use the respective feature accommodated by your backup provider to reinstate all encrypted items.
Option 2: Recovery toolsThe research of ODIN virus reveals an important fact about the way it processes the victim’s data: it deletes the original files, and it’s actually their copies that are encrypted. In the meanwhile, it is common knowledge that anything erased from a computer doesn’t completely vanish and can be dragged out of memory via certain techniques. Recovery applications are capable of doing this, so this method is surely worth a try.
Option 3: Shadow CopiesThe Windows operating system incorporates a technology referred to as the Volume Snapshot Service, or VSS, which performs files or volumes backup routine automatically. One critical prerequisite in this regard is to have the System Restore feature toggled on. In case it has been active, some data segments can be successfully recovered.
You may perform this activity with the Previous Versions functionality, which is built into the OS, or by means of special applications that will do the job automatically.
-
Previous Versions feature
Right-click on a file and choose Properties in the context menu. Find a tab named Previous Versions and click on it to view the last automatic backup that was made. Depending on a preferred action, click Restore to get the file recovered to its original location, or click Copy and indicate a new directory.

-
Shadow Explorer applet
It’s remarkably easy to manage Previous Versions of files and folders with automated tools like Shadow Explorer. This program is free to use. Download and install it, let it come up with a profile of the file hierarchy on the computer, and get down to the restoration proper. You can select a drive name on the list, then right-click on the files or folders to recover, and click Export to proceed.

Did the problem go away? Check and see
Computer threats like ransomware may be stealthier than you can imagine, skillfully obfuscating their components inside a compromised computer to evade removal. Therefore, by running an additional security scan you will dot the i’s and cross the t’s in terms of the cleanup.



