Table of Contents
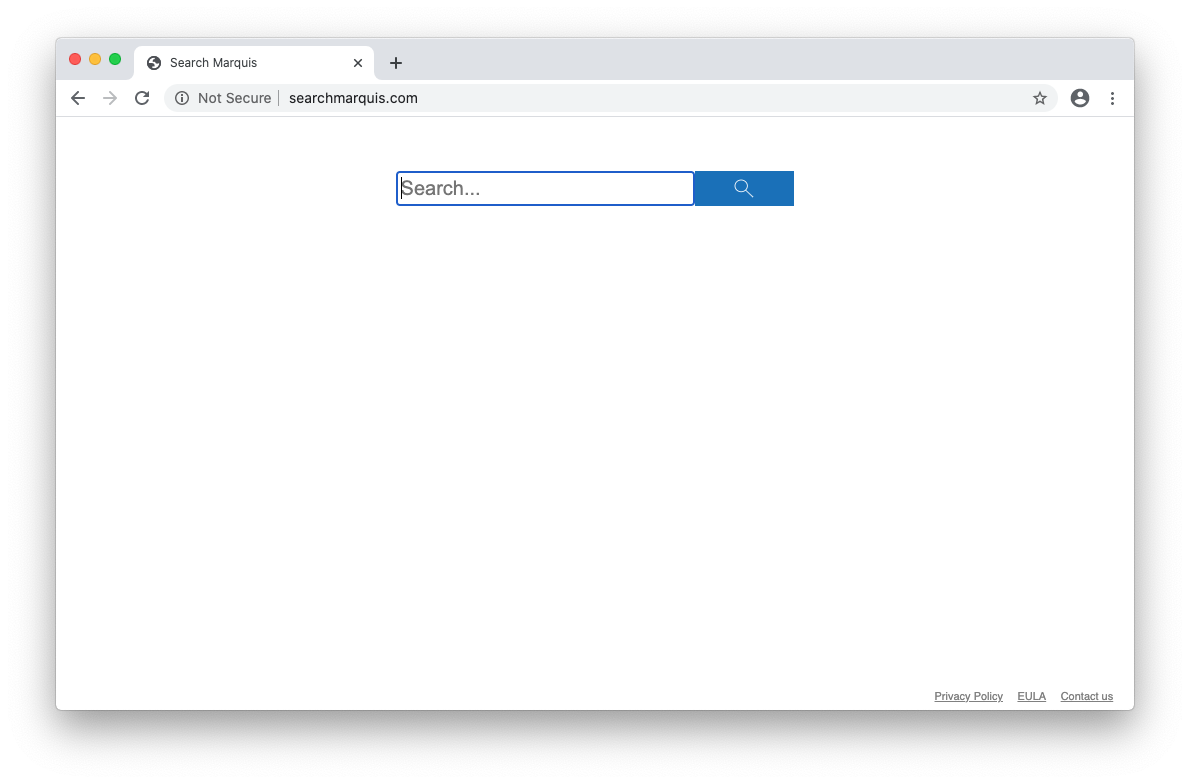
Amidst the security threats Mac users should be worried about, browser hijackers like SearchMarquis.com really stand out due to their aggressive essence.
August 2023 update
What is the Search Marquis Mac virus?
Browser hijacker that has been making big waves in the macOS community is the Search Marquis virus. Originating from a lineage of notorious browser redirect culprits, this malware has been causing significant distress among Mac users. But what exactly is the Search Marquis virus, and why should Mac users be concerned? The Search Marquis virus, at its core, is a deceptive software designed to manipulate browser settings without the user’s consent. The primary objective behind this malicious activity is monetization. By redirecting users, the perpetrators can generate ad revenue, gather user data, or even promote other malicious software. The stealthy nature of its infiltration makes it even more dangerous. Often bundled with seemingly harmless software packages, the Search Marquis virus sneaks into systems, catching users off-guard. Once inside, it employs a series of sophisticated techniques to ensure its persistence, making manual removal a daunting task for the average user.
If you happen to think Mac malware is a marginal thing, the SearchMarquis.com baddie will prove you wrong. In fact, malicious apps targeting devices that run the indisputably awesome macOS operating system have been around for quite some time, and they have become mainstream over the past few years. The strain mentioned above is a prime example of the multi-pronged cybercriminals campaigns from this category. Its adverse effects span browser interference for the most part, but the ostensibly limited attack surface is a false comfort. The victims are stuck with extremely annoying redirects to SearchMarquis.com website that are being triggered in their default browser for seemingly no obvious reason. There is a clear-cut cause, though. A piece of malware is behind every such quandary. The goal is to intercept Mac users’ Internet traffic and tunnel it towards another service via an ad network. This guile allows the crooks to monetize the attack to the fullest.
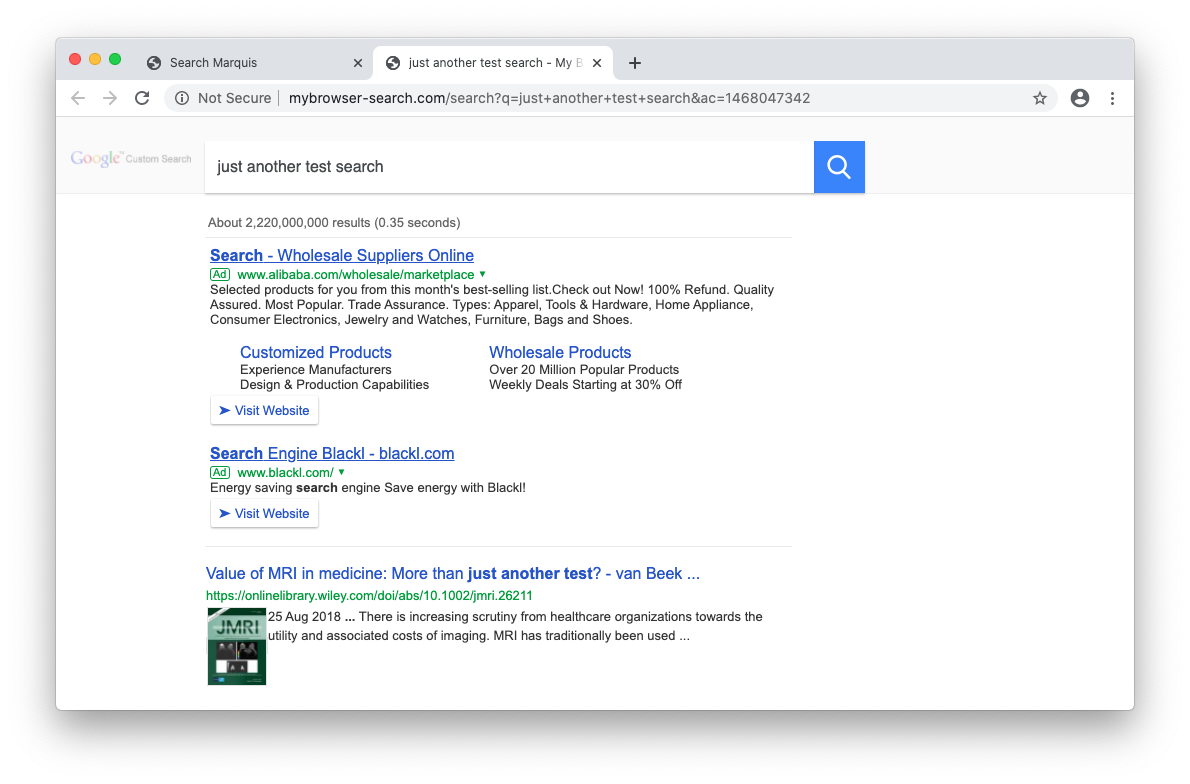
Which landing page is involved in this campaign? The answer might appear surprising to some – it’s Bing, the search engine provided by Microsoft. The whys and wherefores of such a weird stratagem lie in the very gist of the hijack. Like it has been mentioned, the route of the twisted web navigation in this scenario is more complex than it might appear. Technically, the victim departs from SearchMarquis.com and then hits several auxiliary domains, including the notorious SearchBaron.com, prior to landing on Bing.com. These visits are almost unnoticeable and can only be seen momentarily in the status bar at the bottom of the browser window. So, Bing is just a cover-up that’s supposed to add a hue of legitimacy to the electronic raid. What matters to the villains is the series of interstitial addresses being resolved along the way. The latest tweak to the Search Marquis browser hijacking wave has introduced several extra domains to the mix. It took root in the summer 2020. In addition to Bing as the landing page, the malware operators started using mybrowser-search.com. As the screen capture below demonstrates, this service leverages Google Custom Search API instead of returning results of its own.
The trespass of the SearchMarquis.com virus is a covert encounter. Its payload is usually obfuscated by an install client that seems to facilitate the setup of an inoffensive app. The nifty program – usually freeware – is just the tip of the iceberg that distracts the Mac user from the ruse. It turns out that, by default, the bundle includes complementary items, the Search Marquis junk being among them. Steering clear of problems in this situation is ridiculously easy – all it takes is opting for custom install, which should reveal the entire list of the promoted applications and lets the user uncheck the redundant ones. However, prudence in this regard is hardly ever the case, which means people just click through and finish the process, only to realize that the wonderful free program has got company.
When up and running, the virus reorganizes the system configuration in such a way that the victim’s default web browser – Safari, Google Chrome, or Mozilla Firefox – returns SearchMarquis.com every time they try to open their homepage or favorite search engine. The settings replacement trick isn’t sophisticated per se, but the peculiar implementation with persistence at its core is an obstacle to the repair. In other words, switching back to the right web surfing preferences manually won’t help, because the virus will reapply the unwanted adjustments.
This is largely due to the creation of a dubious configuration profile on a plagued Mac as part of the attack. With this smart trick up its sleeve, the malicious program controls browser behavior and puts unwanted preferences back into effect after the victim’s attempts to revert to normal settings. In Google Chrome, for instance, this technique causes a new enterprise policy to appear, which is tough to override. One of the prominent symptoms of this tampering is an inscription saying “Managed by your organization” in the browser’s configuration drop-down menu. In the aftermath of this attack, the affected browser will be instructed to resolve SearchMarquis.com off and on, which in its turn will be redirecting all searches to Bing while “touching” a few extra domains. It is, obviously, in nobody’s interest to endure such a mess. Here’s what to do to block the irritating browser redirects.
Automatic removal of SearchMarquis.com redirect virus from Mac
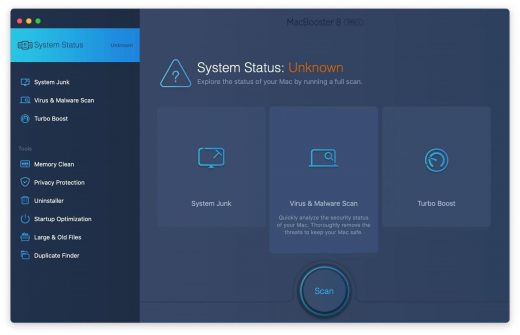
If this threat has infected your Mac, the most effective way to get rid of it is to use an automatic cleaning tool. The main benefit of taking this route is that the security application will accurately pinpoint and remove all the malicious files, including hidden components that could be difficult to find and erase manually. MacBooster is an award-winning solution that makes this process easy and fast. Follow the steps below to make the most of its malware removal and optimization power:
1. Download and install MacBooster onto your Mac.Download SearchMarquis.com virus removal tool
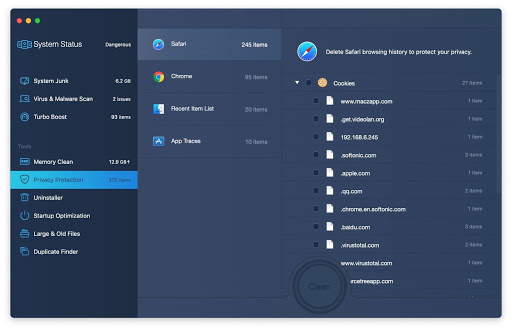
2. Open the tool and click on the Scan button on its home screen called System Status. The application will check your Mac for viruses and malware, memory issues, and junk files. 3. Once the scan is completed, MacBooster will display a report listing all the security and performance problems detected on your computer. Click on the Fix button to remove the malicious items and fine-tune your Mac’s performance.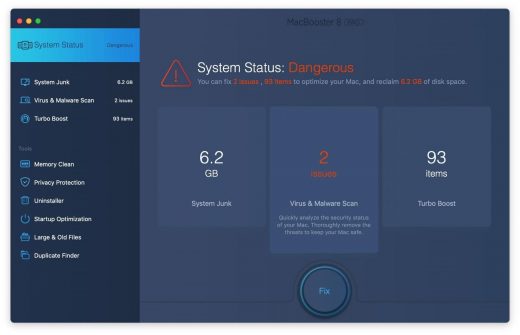 4. To address the after-effects of SearchMarquis.com virus activity in the web browser, select the Privacy Protection feature in MacBooster sidebar, choose your default browser, and click on the
Clean button at the bottom. This will delete unwanted cookies and other items affecting the browser behavior.
4. To address the after-effects of SearchMarquis.com virus activity in the web browser, select the Privacy Protection feature in MacBooster sidebar, choose your default browser, and click on the
Clean button at the bottom. This will delete unwanted cookies and other items affecting the browser behavior.
The SearchMarquis.com virus shouldn’t be messing around with your Mac any longer. Be advised, though, that your default browser may still be redirected to dubious pages until you rectify its settings (the reset procedure will be described further down).
SearchMarquis.com redirect virus manual removal from Mac
The gist of this section is to walk you through the process of deleting all non-obfuscated files related to the SearchMarquis.com virus Mac. It’s best to perform the cleanup in the order specified below.
-
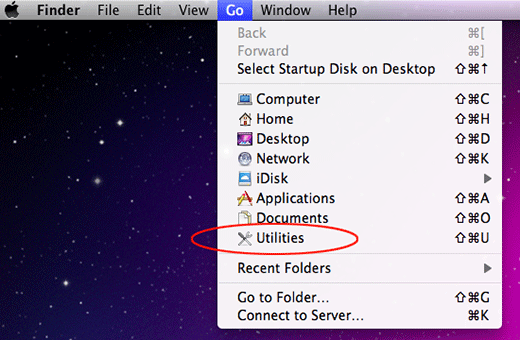
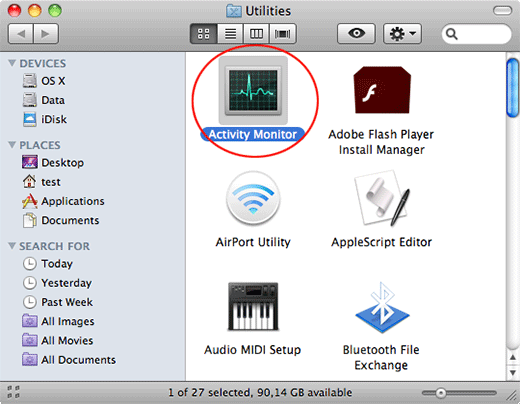
Click the Go icon in Finder and select Utilities on the list

-
Find and select the Activity Monitor under Utilities

-
In the Activity Monitor, scrutinize the running processes for one that consumes lots of CPU and looks suspicious. Once the likely baddie is found, select it and click the Quit Process icon. An additional
confirmation dialog will pop up – click Force Quit on it

-
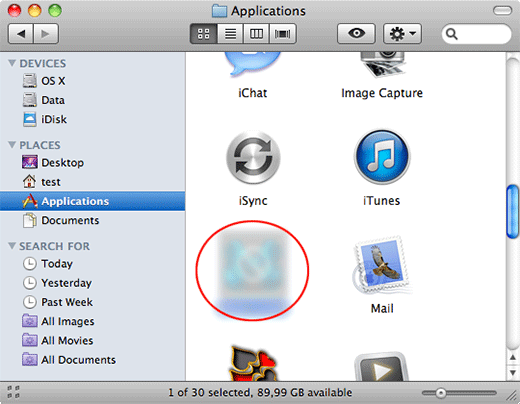
Now, go to Applications under the Go menu

-
What you need to do is scroll down the list of installed apps in search of the malicious item. It could be a program with a gibberish name or one that ended up on your Mac beyond your awareness

-
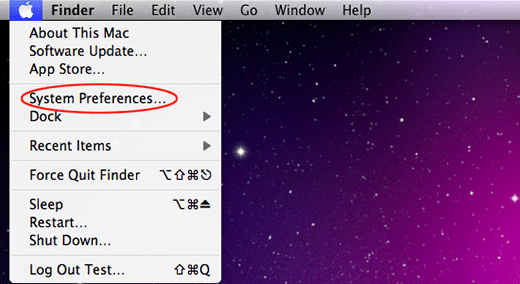
Go to System Preferences as shown below

-
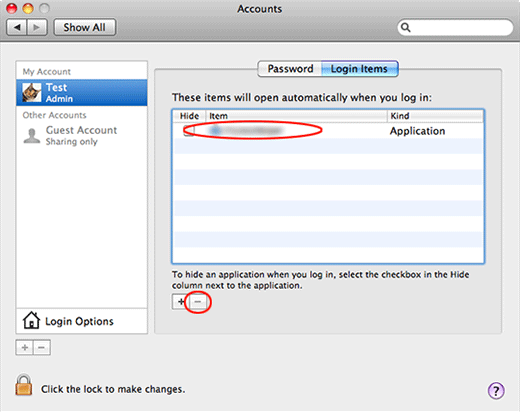
Select Accounts, then Login Items. You will see all the apps that run as part of the Mac startup process. Find the infection and remove it from the list by means of the “minus” icon

Now that you have suppressed the virus proper, you need to fix the problem in Safari. The browser defaults continue to be set to SearchMarquis.com, therefore the repair requires some manual configuration tweaking.
Remove SearchMarquis.com redirects from affected browser on Mac
The optimal troubleshooting method boils down to resetting the browser, which will undo all changes made by the infection or any third-party plugin without your permission. Here’s how to do it:
Reset Safari to its defaults
-
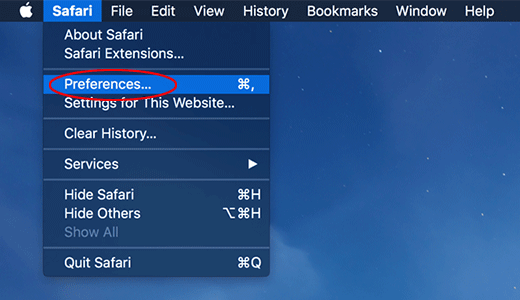
Go to Safari menu bar and select Preferences again on the drop-down list

-
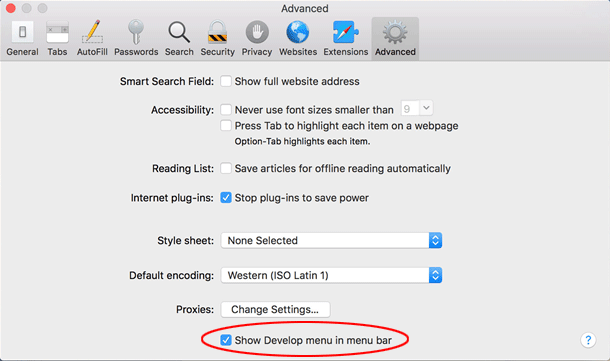
Go to Advanced tab and enable the option that says Show Develop menu in menu bar

-
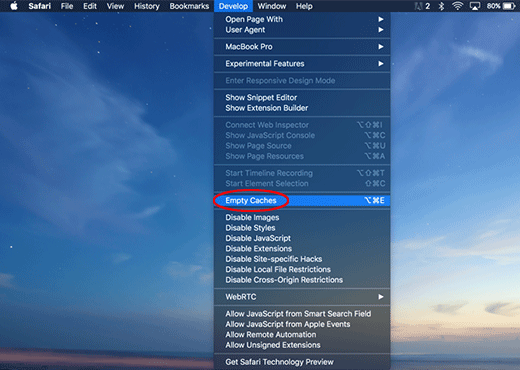
Now you will see the extra Develop menu in your Safari menu bar. Click it and select Empty Caches as shown below

-
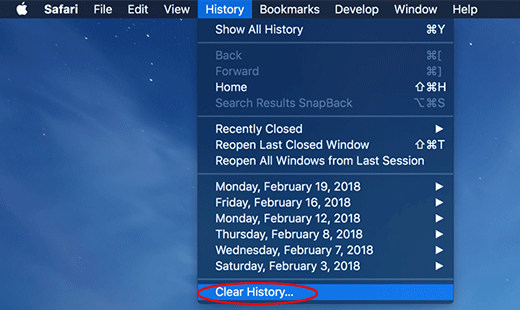
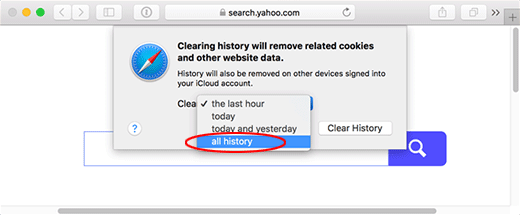
Do some test browsing to see if things are okay now and whether the malware is gone. If the issue is still there, you may need to additionally clear your browsing history in Safari. In Safari menu bar, select
History and click Clear History

-
The browser will display a dialog so that you can select the required period you would like to clear history for. Select all history on the list and click the Clear History button

-
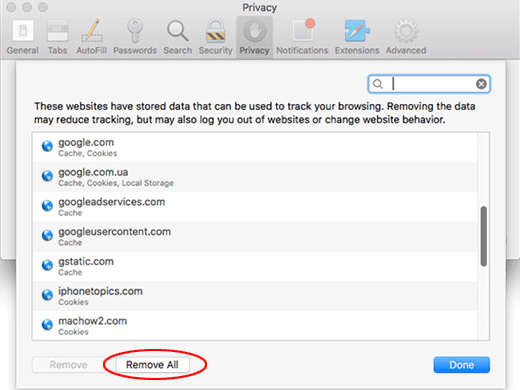
In case Safari is still acting up due to malware interference, there is one more thing you can try. Once again, go to Preferences from the Safari menu bar and select the Privacy tab
this time. Click Manage Website Data

-
When Safari generates a full list of sites that have stored your browsing data, go ahead and click Remove All

- Confirm by hitting the Done button.
Reset Google Chrome
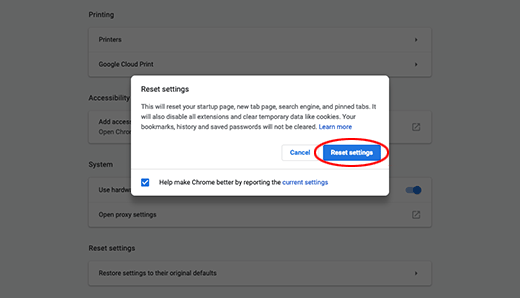
- Click More (⁝ icon) at the top right part of the Chrome window and select Settings
- Find the Advanced section on the Settings screen and expand it
-
Locate the Reset settings subsection and click Restore settings to their original defaults

- Google Chrome will display a popup dialog asking you to confirm the reset. Click the Reset settings button on it. Now, restart the browser and ascertain that the problem has been fixed.
Refresh Mozilla Firefox
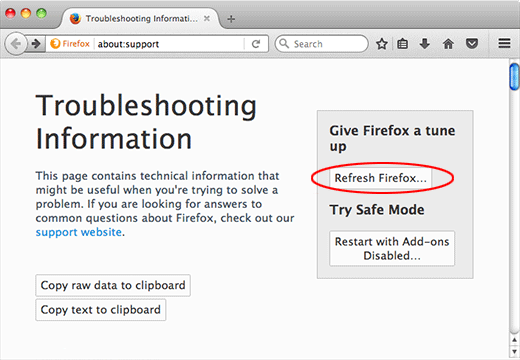
- Go to Help -> Troubleshooting Information, or type about:support in the Firefox URL bar
-
Once the Troubleshooting Information screen appears, find and click the Refresh Firefox button as shown

- Confirm the browser refresh on a dialog that will appear. Restart Firefox and check it for signs of malware tampering.