Table of Contents
Get up-to-date advice on restoring files encrypted by CryptXXX v3.x, the latest edition of the widespread ransom Trojan released with quite a few enhancements.
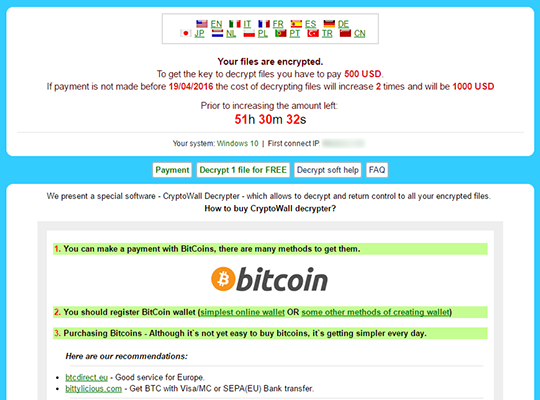
The crypto ransomware under consideration isn’t brand-new, but its authors appear to be continuously working on code improvements and have rolled out 3 updates over the course of a month. The recent variant has a number of critical changes under the hood, including more efficient implementation of the crypto and the wording of ransom notes. Once the plague has completed the data encoding part of its mission, it presents recovery instructions in the following files: !Recovery_[victim ID].txt, !Recovery_[victim ID].html and !Recovery_[victim ID].bmp. The string in brackets stands for the personal identifier that the virus allots to every infected user during the compromise. These documents will appear on the desktop and inside each folder with encrypted entities.
![!Recovery_[victim ID].html ransom instructions !Recovery_[victim ID].html ransom instructions](https://keonesoftware.com/wp-content/uploads/de_crypt_readme-html.png)
As before, CryptXXX 3.0 targets the same range of file formats on infected PCs. These include all sorts of Microsoft Office files, media objects, databases, PDFs and tens of other entities. To locate these, the ransomware recursively scans the local drives, removable devices and mapped network shares, comparing the encountered items’ extensions against as hard-coded list of format identifiers. When done finding the victim’s personal data, the Trojan leverages a strong combo of RSA-4096 and RC4 (Rivest Cipher 4) to encrypt all matches. Not only do these objects become inaccessible, but they also get the .cryp1 extension attached to the original full filenames.
As opposed to the previous 2 versions, CryptXXX v3.0 cannot be cracked with Kaspersky RannohDecryptor. The ransomware developers tried so hard to prevent the tool from recovering data for free that they rendered their own paid decrypt solution non-functional. This bug has been reportedly fixed at the time of this writing. Enthusiasts and researchers from different security labs claim they can decrypt the file byte blocks enciphered with RC4, but RSA blocks aren’t recoverable without the private key.
The amount of money that CryptXXX v3.x distributors demand for recovery is in the range of 1.2 BTC, or approximately 500 USD. Victims can get 1 file decrypted for free. If the initial deadline for payment expires, the sum goes up two times. Considering the glitches that users have run into with the functionality of the criminals’ decryptor, paying is not an option, moreover, it’s a terrible idea from an ethical perspective. The use of Shadow Volume Copies and recovery suites instead is definitely a worthwhile thing for a start.
Automatic removal of CryptXXX 3.0 virus
When it comes to handling infections like this one, using a reputable cleaning tool is the place to start. Sticking to this workflow ensures that every component of the adware gets found and eradicated from the affected computer.
1. Download and install the cleaning tool and click the Start Computer Scan button Download CryptXXX 3.0 removal tool
2. The wait is worth it. Once the scan completes, you will see a report listing all malicious or potentially unwanted objects detected on your PC. Go ahead and click the Fix Threats option in order to get CryptXXX 3.0 automatically uninstalled from your machine. The following steps are intended to restore the encrypted files.
Recover .cryp1 files ciphered by CryptXXX v3.0 the ransomware
Removing the infection proper is only a part of the fix, because the seized personal information will stay encrypted regardless. Review and try the methods below to get a chance of restoring the files.
Option 1: BackupsThe cloud works wonders when it comes to troubleshooting in the framework of ransomware assault. If you have been keeping data backups in a remote place, just use the respective feature accommodated by your backup provider to reinstate all encrypted items.
Option 2: Recovery toolsThe research of CryptXXX 3.0 virus reveals an important fact about the way it processes the victim’s data: it deletes the original files, and it’s actually their copies that are encrypted. In the meanwhile, it is common knowledge that anything erased from a computer doesn’t completely vanish and can be dragged out of memory via certain techniques. Recovery applications are capable of doing this, so this method is surely worth a try.
Option 3: Shadow CopiesThe Windows operating system incorporates a technology referred to as the Volume Snapshot Service, or VSS, which performs files or volumes backup routine automatically. One critical prerequisite in this regard is to have the System Restore feature toggled on. In case it has been active, some data segments can be successfully recovered.
You may perform this activity with the Previous Versions functionality, which is built into the OS, or by means of special applications that will do the job automatically.
-
Previous Versions feature
Right-click on a file and choose Properties in the context menu. Find a tab named Previous Versions and click on it to view the last automatic backup that was made. Depending on a preferred action, click Restore to get the file recovered to its original location, or click Copy and indicate a new directory.

-
Shadow Explorer applet
It’s remarkably easy to manage Previous Versions of files and folders with automated tools like Shadow Explorer. This program is free to use. Download and install it, let it come up with a profile of the file hierarchy on the computer, and get down to the restoration proper. You can select a drive name on the list, then right-click on the files or folders to recover, and click Export to proceed.

Did the problem go away? Check and see
Computer threats like ransomware may be stealthier than you can imagine, skillfully obfuscating their components inside a compromised computer to evade removal. Therefore, by running an additional security scan you will dot the i’s and cross the t’s in terms of the cleanup.



