Table of Contents
The breaking news in the cyber world is the emergence of the new crypto virus developed 100% from JavaScript, which cloaks a huge risk of expansion.
The name of the computer program that shall be dissected in this post is quite verbose. It’s RAA ransomware. The associations that come to mind aren’t positive, to put it mildly; and it turns out that the first impression is accurate. This defiant denomination reflects the app’s genuine gist, which consists in extortion activity. The JavaScript based RAA ransomware parasite in question encrypts one’s personal files and asks for a payment to be sent so that the locked information can be recovered. The pest uses Advanced Encryption Standard (AES-256) to freeze 16 file types including documents, videos, audio content and pictures, which basically means that none of these can be restored via decoding techniques of any sort. The cost of this disgusting ‘service’ varies, but it’s around 0.39 Bitcoin most of the time.
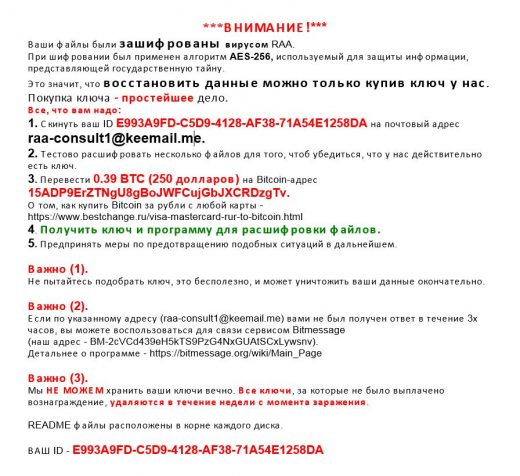
As it has already been mentioned, there are things about RAA ransomware that aren’t invariable. The size of the ransom depends on how insatiable the specific malicious distributor is when it comes to money. Here’s the thing: this infection is one of the few that are based on a ‘malware as a service’ model. What this means is pretty much any person can sign up with the respective affiliate platform by means of a secure Tor (.onion) page online. The easy-to-use dashboard allows the would-be criminal to configure their custom version of the ransomware by setting such parameters as the BTC amount to ask, the time of lockscreen appearance, the type of the message box and a few more. At the end of the day, the fraudster gets a fine-tuned build in a few keystrokes and clicks on the mouse.
RAA ransomware does not launch an executable if the phishing-backed contamination of a computer takes place. It tries to masquerade pretending to be a MS Word file. Upon a closer inspection, the above-mentioned file turns out to be a standard JS file, which denotes a framework allowing cross-platform software development. This fact should be taken very seriously, because the JavaScript code behind RAA ransomware can be changed so that Mac and Linux systems will also be vulnerable to the crypto attack.
Additionally, this virus delivers a password stealer called Pony that can do a lot of harm with unknown consequences.
Though no tools can decrypt files affected by the RAA JavaScript ransom Trojan, a few tips are worth putting into practice for the sake of recovery.
Automatic removal of the RAA JavaScript ransomware ransomware
When it comes to handling infections like this one, using a reputable cleaning tool is the place to start. Sticking to this workflow ensures that every component of the adware gets found and eradicated from the affected computer.
1. Download and install the cleaning tool and click the Start Computer Scan button Download RAA JavaScript removal tool
2. The wait is worth it. Once the scan completes, you will see a report listing all malicious or potentially unwanted objects detected on your PC. Go ahead and click the Fix Threats option in order to get RAA JavaScript automatically uninstalled from your machine. The following steps are intended to restore the encrypted files.
Recover files locked by RAA JavaScript ransomware ransomware
Removing the infection proper is only a part of the fix, because the seized personal information will stay encrypted regardless. Review and try the methods below to get a chance of restoring the files.
Option 1: BackupsThe cloud works wonders when it comes to troubleshooting in the framework of ransomware assault. If you have been keeping data backups in a remote place, just use the respective feature accommodated by your backup provider to reinstate all encrypted items.
Option 2: Recovery toolsThe research of RAA JavaScript virus reveals an important fact about the way it processes the victim’s data: it deletes the original files, and it’s actually their copies that are encrypted. In the meanwhile, it is common knowledge that anything erased from a computer doesn’t completely vanish and can be dragged out of memory via certain techniques. Recovery applications are capable of doing this, so this method is surely worth a try.
Option 3: Shadow CopiesThe Windows operating system incorporates a technology referred to as the Volume Snapshot Service, or VSS, which performs files or volumes backup routine automatically. One critical prerequisite in this regard is to have the System Restore feature toggled on. In case it has been active, some data segments can be successfully recovered.
You may perform this activity with the Previous Versions functionality, which is built into the OS, or by means of special applications that will do the job automatically.
-
Previous Versions feature
Right-click on a file and choose Properties in the context menu. Find a tab named Previous Versions and click on it to view the last automatic backup that was made. Depending on a preferred action, click Restore to get the file recovered to its original location, or click Copy and indicate a new directory.

-
Shadow Explorer applet
It’s remarkably easy to manage Previous Versions of files and folders with automated tools like Shadow Explorer. This program is free to use. Download and install it, let it come up with a profile of the file hierarchy on the computer, and get down to the restoration proper. You can select a drive name on the list, then right-click on the files or folders to recover, and click Export to proceed.

Did the problem go away? Check and see
Computer threats like ransomware may be stealthier than you can imagine, skillfully obfuscating their components inside a compromised computer to evade removal. Therefore, by running an additional security scan you will dot the i’s and cross the t’s in terms of the cleanup.



