Table of Contents
This guide covers the process and aftermath of Cerber Ransomware Decryptor attack, which is a new edition of the newsmaking, widespread crypto infection.
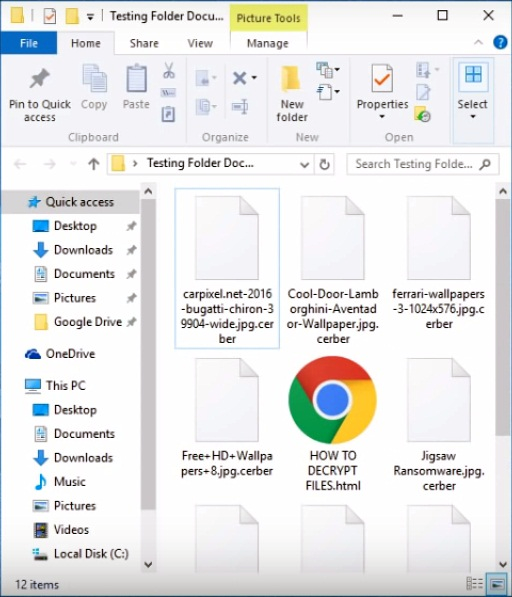
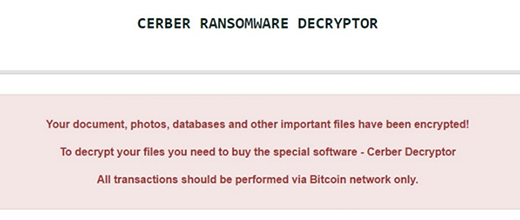
Prior to last week, the ransom Trojan called Cerber had been a record-breaker in a way. Having emerged in early March 2016, it had operated in its original form and shape for more than four months, which is quite unusual in the world of crypto viruses most of which are updated frequently. This state of things has changed, though. The recent revamp of the offending code in question came out dramatic. The troublemaking program is now referred to as “Cerber Ransomware Decryptor”, which is the name indicated in the ransom notes. Furthermore, the previously used combo of recovery instruction documents titled # DECRYPT MY FILES #.html (.vbs, .txt) have been replaced with a single file named “HOW TO DECRYPT FILES.html”, a copy of which is dropped into every folder with ciphered items. It opens up via the default web browser on the infected system.
On the one hand, this renders the user interaction part of the compromise simpler and more streamlined. On the other, though, this strain doesn’t appear to be that unique anymore. It used to literally speak to its victims by means of a script in the above-mentioned .vbs edition of the ransom notes. Now Cerber seems to be just one of the many file-encrypting threats out there, with no particular zest under the hood. And yet, it’s using the same powerful distribution channels that keep the infection rate high. Furthermore, the data encryption routine has yet to be cracked – security experts have been unsuccessful in doing it thus far.
As before, this crypto ransomware uses AES-256 algorithm to encode its victims’ data. A byproduct of this file scrambling is the appending of “.cerber”, “.cerber2”, “.cerber3” etc. string to filenames, which follows the original extension. For example, the infection turns an entry named “vehicle.jpg” into “vehicle.jpg.cerber”. Of course, none of these objects can be accessed due to the flawless implementation of cryptography.
The verbal filling of the Cerber Ransomware Decryptor recovery instructions (HOW TO DECRYPT FILES.html) has changed as well. Whereas the document still says, “Your documents, photos, databases and other important files have been encrypted”, it continues as follows, “To decrypt your files you need to buy the special software – Cerber Decryptor. All transactions should be performed via Bitcoin network only.” The message also emphasizes that “any attempts to get back your files with the third-party tools can be fatal for your encrypted files.”
The size of the ransom has become lower compared to the previous variant. While it used to amount to 1.24 Bitcoins, now it’s 0.4 Bitcoins, or about 240 USD. The 7-day deadline for submitting this money and subsequent increase of the ransom are no longer the case. This is still cold comfort, though. The infected users face a tough dilemma: to buy their personal data out by paying to the extortionists, or lose the information. However, there is one more option that’s definitely worth a shot. Read the part below and follow the instructions to implement the workaround.
Automatic removal of Cerber Ransomware virus
When it comes to handling infections like this one, using a reputable cleaning tool is the place to start. Sticking to this workflow ensures that every component of the adware gets found and eradicated from the affected computer.
1. Download and install the cleaning tool and click the Start Computer Scan button Download Cerber removal tool
2. The wait is worth it. Once the scan completes, you will see a report listing all malicious or potentially unwanted objects detected on your PC. Go ahead and click the Fix Threats option in order to get Cerber automatically uninstalled from your machine. The following steps are intended to restore the encrypted files.
Recover files ciphered by Cerber Ransomware virus
Removing the infection proper is only a part of the fix, because the seized personal information will stay encrypted regardless. Review and try the methods below to get a chance of restoring the files.
Option 1: BackupsThe cloud works wonders when it comes to troubleshooting in the framework of ransomware assault. If you have been keeping data backups in a remote place, just use the respective feature accommodated by your backup provider to reinstate all encrypted items.
Option 2: Recovery toolsThe research of Cerber virus reveals an important fact about the way it processes the victim’s data: it deletes the original files, and it’s actually their copies that are encrypted. In the meanwhile, it is common knowledge that anything erased from a computer doesn’t completely vanish and can be dragged out of memory via certain techniques. Recovery applications are capable of doing this, so this method is surely worth a try.
Option 3: Shadow CopiesThe Windows operating system incorporates a technology referred to as the Volume Snapshot Service, or VSS, which performs files or volumes backup routine automatically. One critical prerequisite in this regard is to have the System Restore feature toggled on. In case it has been active, some data segments can be successfully recovered.
You may perform this activity with the Previous Versions functionality, which is built into the OS, or by means of special applications that will do the job automatically.
-
Previous Versions feature
Right-click on a file and choose Properties in the context menu. Find a tab named Previous Versions and click on it to view the last automatic backup that was made. Depending on a preferred action, click Restore to get the file recovered to its original location, or click Copy and indicate a new directory.

-
Shadow Explorer applet
It’s remarkably easy to manage Previous Versions of files and folders with automated tools like Shadow Explorer. This program is free to use. Download and install it, let it come up with a profile of the file hierarchy on the computer, and get down to the restoration proper. You can select a drive name on the list, then right-click on the files or folders to recover, and click Export to proceed.

Did the problem go away? Check and see
Computer threats like ransomware may be stealthier than you can imagine, skillfully obfuscating their components inside a compromised computer to evade removal. Therefore, by running an additional security scan you will dot the i’s and cross the t’s in terms of the cleanup.