Table of Contents
Even with significant resources on their hands, antimalware labs and law enforcement are still unable to efficiently tackle ransomware threats like Cerber.
It has been about a month since the first incidents of contamination by the Cerber file-encrypting malware were spotted. Back then, it hit the headlines due to a very unique feature built into its code – the ransomware could communicate its demands by speaking to victims. Although this may seem like a climax of sophistication, the way the audio functionality works isn’t much of a rocket science. The cybercriminals simply added a VBScript edition of the ransom notes, which generates sound when activated. Therefore, the ostensible fineness and complexity of this sample doesn’t make a whole lot of difference in terms of the crypto part of its activity as well as the recovery options for infected Windows users.
The Cerber virus uses the Advanced Encryption Standard (AES-256) to prevent its victims from opening their personal files. It targets data that’s not critical for normal work of the operating system, which is a reasonable approach on the ransomware operators’ end otherwise the contaminated users wouldn’t even get to the fee payment part. Interestingly, the pest functions with some geographic limitations, discontinuing the attack if the user is from one of the former Soviet Union countries.
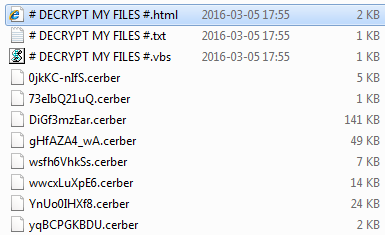
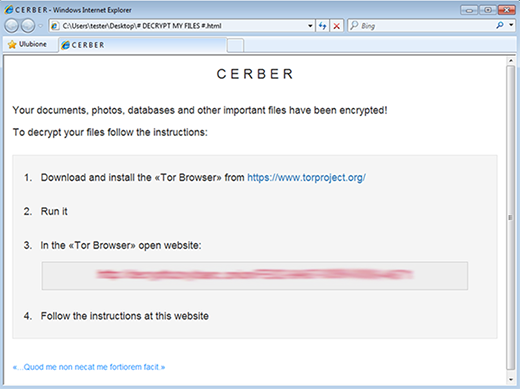
When encrypting files on the local disks and mapped network shares, the Trojan also adds the .cerber extension to each one. Furthermore, the filenames are skewed as well so that the person doesn’t know where a specific file is. Inside every affected folder as well as on the desktop, it creates three documents: # Decrypt My Files #.html, # Decrypt My Files #.txt, and the above-mentioned # Decrypt My Files #.vbs. The purpose of these objects is to inform the user about the attack. For instance, the HTML version says “Your documents, photos, databases and other important files have been encrypted!” According to these notes, the victim must use the Tor Browser to open a specific website and follow instructions there. The demands are as follows: the user has to pay 1.24 Bitcoins or lose all files.
Just like its counterparts, the infection runs from AppData, where it creates a random named folder after the compromise has taken place. When launched for the first time, the malicious executable triggers a command to reboot the machine into Safe Mode with Networking. Then, it toggles Windows settings so that it further launches upon boot time and runs at certain brief intervals. This part being completed, a phony shutdown alert triggers another system restart followed by the encryption process in the background and the extortion activity proper.
According to recent reports, the distribution of Cerber ransomware involves an Adobe Flash Player vulnerability. In other words, the mean hackers deposit an exploit on compromised or malicious websites, and visitors with unpatched Flash Player loophole get infected without realizing it. So it’s highly recommended to update said software regularly. As far as the troubleshooting goes, Cerber is currently impossible to decrypt. However, there are mechanisms to try and restore some files.
Automatic removal of Cerber virus
When it comes to handling infections like this one, using a reputable cleaning tool is the place to start. Sticking to this workflow ensures that every component of the adware gets found and eradicated from the affected computer.
1. Download and install the cleaning tool and click the Start Computer Scan button Download Cerber removal tool
2. The wait is worth it. Once the scan completes, you will see a report listing all malicious or potentially unwanted objects detected on your PC. Go ahead and click the Fix Threats option in order to get Cerber automatically uninstalled from your machine. The following steps are intended to restore the encrypted files.
Recover files locked by the ransomware
Removing the infection proper is only a part of the fix, because the seized personal information will stay encrypted regardless. Review and try the methods below to get a chance of restoring the files.
Option 1: BackupsThe cloud works wonders when it comes to troubleshooting in the framework of ransomware assault. If you have been keeping data backups in a remote place, just use the respective feature accommodated by your backup provider to reinstate all encrypted items.
Option 2: Recovery toolsThe research of Cerber virus reveals an important fact about the way it processes the victim’s data: it deletes the original files, and it’s actually their copies that are encrypted. In the meanwhile, it is common knowledge that anything erased from a computer doesn’t completely vanish and can be dragged out of memory via certain techniques. Recovery applications are capable of doing this, so this method is surely worth a try.
Option 3: Shadow CopiesThe Windows operating system incorporates a technology referred to as the Volume Snapshot Service, or VSS, which performs files or volumes backup routine automatically. One critical prerequisite in this regard is to have the System Restore feature toggled on. In case it has been active, some data segments can be successfully recovered.
You may perform this activity with the Previous Versions functionality, which is built into the OS, or by means of special applications that will do the job automatically.
-
Previous Versions feature
Right-click on a file and choose Properties in the context menu. Find a tab named Previous Versions and click on it to view the last automatic backup that was made. Depending on a preferred action, click Restore to get the file recovered to its original location, or click Copy and indicate a new directory.

-
Shadow Explorer applet
It’s remarkably easy to manage Previous Versions of files and folders with automated tools like Shadow Explorer. This program is free to use. Download and install it, let it come up with a profile of the file hierarchy on the computer, and get down to the restoration proper. You can select a drive name on the list, then right-click on the files or folders to recover, and click Export to proceed.

Did the problem go away? Check and see
Computer threats like ransomware may be stealthier than you can imagine, skillfully obfuscating their components inside a compromised computer to evade removal. Therefore, by running an additional security scan you will dot the i’s and cross the t’s in terms of the cleanup.




I’m interested in the encryption keys for .cerber files. I’ve sanitized my machine but would still like to recover files. No plan to pay criminals…
Roger,
Unfortunately, there is no way to obtain the private decryption key for encrypted .cerber files other than to pay the ransom, which is a slippery slope. The key is stored on the crooks’ secret Command & Control server. Furthermore, no free decryptor is available as well. Under the circumstances, try the steps listed in this article.