Table of Contents
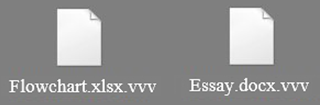
The ransom trojan known as TeslaCrypt got a new feature in the course of the latest upgrade, now assigning a ‘.vvv’ extension to all encrypted filenames.
The basic symptoms of a ransomware assault are quite uniform regardless of the infection breed: the victim’s files get frozen due to crypto that’s applied to them; the ransom note documents get displayed to instruct the person on recovery steps; and a certain amount of Bitcoins is extorted in exchange for the data. With that static set of characteristics in place, each sample involves a number of variable values when going this well-trodden path, such as the type of encryption algorithm, the name of docs holding the payment directions, and the way encoded files’ look is modified. The recent, eighth iteration of TeslaCrypt ransomware distorts all affected documents, spreadsheets, images, movies and archives by altering their extensions to .vvv, which follows the original format marker.
The aftermath of this contamination also presupposes the dropping of ransom directions in the form of how_recover+*.txt and .html objects into the folders whose contents have been encrypted and onto the desktop. As opposed to the vast majority of its counterparts, TeslaCrypt uses the AES standard to make data inaccessible, while the more widespread viruses like CryptoWall and Crypt0L0cker have been employing RSA-2048 instead. Although the Advanced Encryption Standard is considered to be weaker than the latter public-key cryptosystem, it is still strong enough to ensure the victims aren’t able to bypass it. The ransom sum is currently around 500 USD or, to be more specific, the Bitcoin equivalent of this amount. In order to submit it, the user needs to click the personal TOR link which redirects to the Decryption Service site with the respective processing functionality.
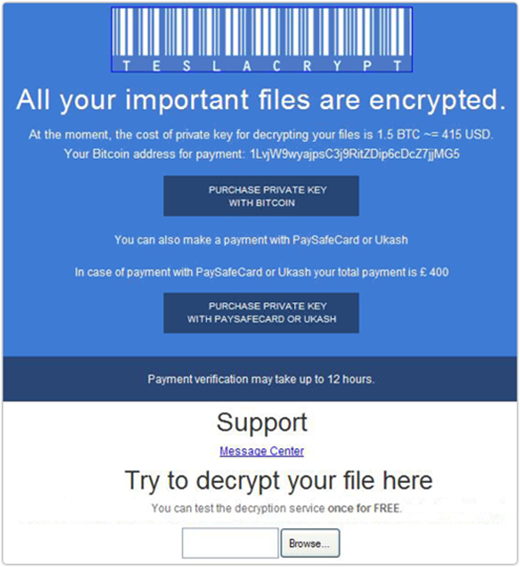
The malware might allow the victim to perform a one-time test of the decrypt service for free, but that’s not the case with all versions. What makes the whole campaign yet more confusing is the fact that some variants of TeslaCrypt can be masqueraded as the aforementioned CryptoWall, while the tech stuffing remains basically the same. From where the user stands, though, this discrepancy doesn’t make much of a difference as they are still forced to either pay the crims or look for workarounds.
The distribution of this sample is still backed by social engineering. Users unknowingly activate the payload when opening an attachment that goes with a phishing email. These messages look like real traffic violation reports, invoices, resumes or shipping notifications. The ZIP files enclosed in them host an obfuscated routine that furtively infects the computer. The hard drive then gets scanned against a list of file extensions so that everything meeting the pre-set criteria is processed with the crypto algorithm. A couple of must-try troubleshooting techniques are provided in the next part of the post, quite likely assisting the infected users in restoring their information.
Automatic removal of the .vvv file virus
When it comes to handling infections like this one, using a reputable cleaning tool is the place to start. Sticking to this workflow ensures that every component of the adware gets found and eradicated from the affected computer.
1. Download and install the cleaning tool and click the Start Computer Scan button Download .vvv file virus removal tool
2. The wait is worth it. Once the scan completes, you will see a report listing all malicious or potentially unwanted objects detected on your PC. Go ahead and click the Fix Threats option in order to get .vvv file virus automatically uninstalled from your machine. The following steps are intended to restore the encrypted files.
Recover files locked by the ransomware
Removing the infection proper is only a part of the fix, because the seized personal information will stay encrypted regardless. Review and try the methods below to get a chance of restoring the files.
Option 1: BackupsThe cloud works wonders when it comes to troubleshooting in the framework of ransomware assault. If you have been keeping data backups in a remote place, just use the respective feature accommodated by your backup provider to reinstate all encrypted items.
Option 2: Recovery toolsThe research of .vvv file virus virus reveals an important fact about the way it processes the victim’s data: it deletes the original files, and it’s actually their copies that are encrypted. In the meanwhile, it is common knowledge that anything erased from a computer doesn’t completely vanish and can be dragged out of memory via certain techniques. Recovery applications are capable of doing this, so this method is surely worth a try.
Option 3: Shadow CopiesThe Windows operating system incorporates a technology referred to as the Volume Snapshot Service, or VSS, which performs files or volumes backup routine automatically. One critical prerequisite in this regard is to have the System Restore feature toggled on. In case it has been active, some data segments can be successfully recovered.
You may perform this activity with the Previous Versions functionality, which is built into the OS, or by means of special applications that will do the job automatically.
-
Previous Versions feature
Right-click on a file and choose Properties in the context menu. Find a tab named Previous Versions and click on it to view the last automatic backup that was made. Depending on a preferred action, click Restore to get the file recovered to its original location, or click Copy and indicate a new directory.

-
Shadow Explorer applet
It’s remarkably easy to manage Previous Versions of files and folders with automated tools like Shadow Explorer. This program is free to use. Download and install it, let it come up with a profile of the file hierarchy on the computer, and get down to the restoration proper. You can select a drive name on the list, then right-click on the files or folders to recover, and click Export to proceed.

Did the problem go away? Check and see
Computer threats like ransomware may be stealthier than you can imagine, skillfully obfuscating their components inside a compromised computer to evade removal. Therefore, by running an additional security scan you will dot the i’s and cross the t’s in terms of the cleanup.



