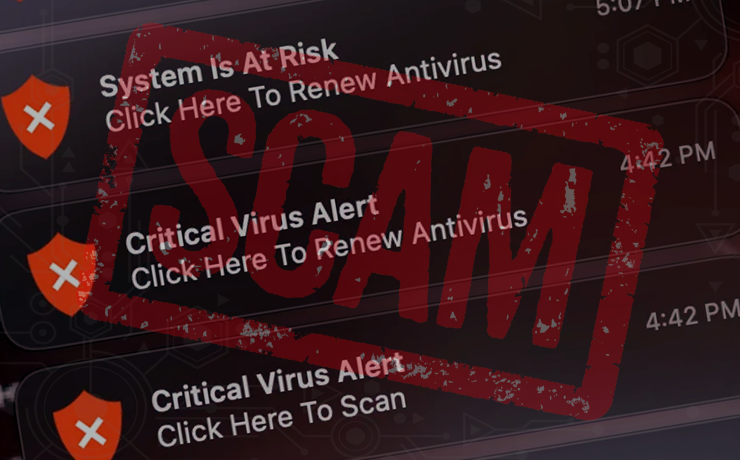
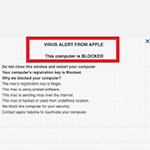
How to remove Critical Virus Alert pop-up on Mac
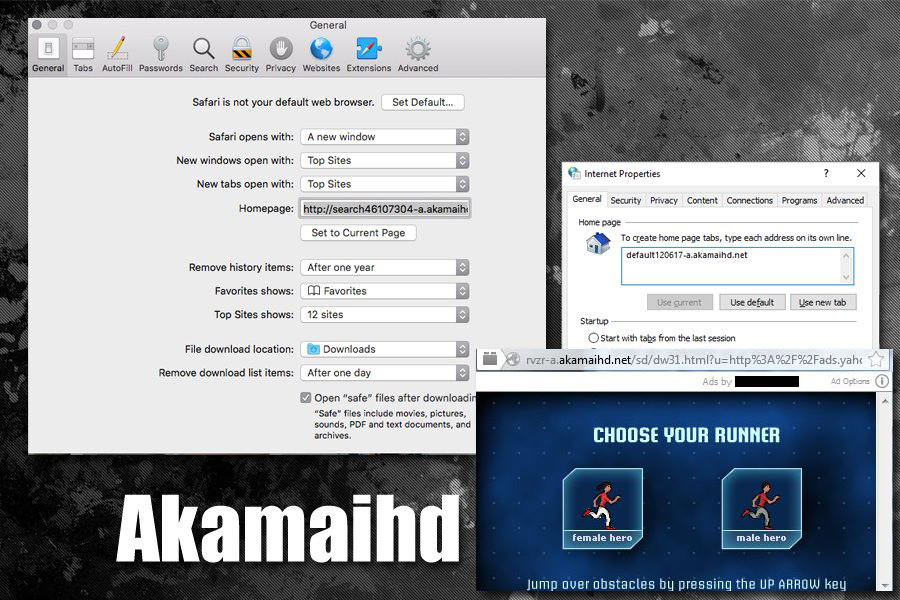
This article delves deep into the anatomy of Critical Virus Alert pop-up scam, its modus operandi, and how users can protect themselves. What is the Critical Virus Alert pop-up scam? The Critical Virus Alert scam is a classic example of this new wave of threats. It starts with a browser redirect, often coupled with social … Read more